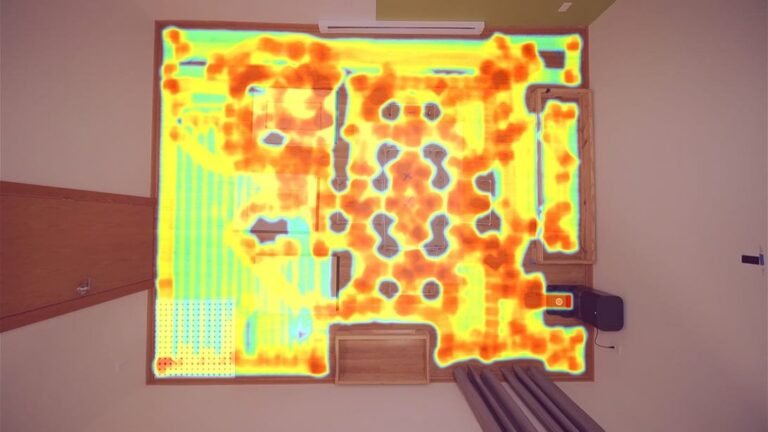
High-end DDR5 RAM kits now costing more than an Nvidia RTX 5090 p…
High End Ddr5 Ram. Did you think a high-end RAM kit would ever cost more than an Nvidia RTX 5090? Well, it does, and that’s truly scary. ry. As we continue to push the boundaries of technological advancements, the cost of high-performance components is skyrocketing, leaving many to wonder if it’s all worth it. The […]
Read more