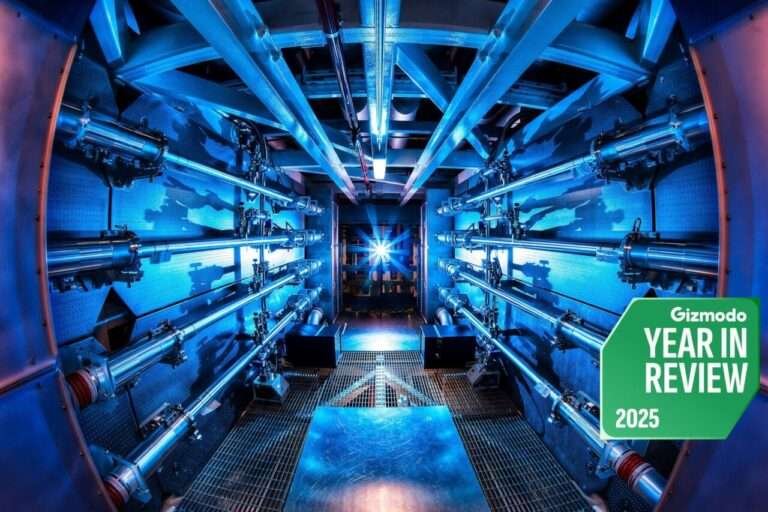
Imagine you’re sipping coffee at a cybersecurity conference in 2017 when a researcher casually drops: *”A scalable quantum computer could turn RSA encryption to dust in a decade.”* The room freezes. No one laughs-because they know this isn’t sci-fi. That quiet moment was my wake-up call about post-quantum cryptography. It wasn’t just theoretical; it was the calm before the storm. And now, nine years later, that storm has arrived. Bain & Company and IBM just announced they’re turning this niche concern into a boardroom imperative. Here’s why the countdown has begun.Understanding Post-Quantum Cryptography: IBM &#… Understanding Post-Quantum Cryptography: IBM &#…Understanding Post-Quantum Cryptography: IBM &#… Understanding Post-Quantum Cryptography: IBM &#…
This isn’t about some distant threat. In my experience, businesses are already facing the fallout. Remember the 2020 NSA memo warning federal agencies about quantum vulnerabilities? They weren’t just being cautious-they were preparing for a reality where post-quantum cryptography isn’t optional. Today’s RSA and ECC (the backbone of 90% of encrypted systems) are like a bank vault with a lock that can be picked with a butter knife. Once a quantum computer with 5,000+ logical qubits arrives-and it’s coming-they’ll be worthless.
post-quantum cryptography: Why now? The post-quantum urgency
The real question isn’t *if* quantum computers will break today’s encryption, but *when*. And the answer is: sooner than most assume. IBM and Bain’s partnership signals that the migration window is closing-fast. Companies in finance, defense, and healthcare aren’t just preparing for the future; they’re dealing with the present. Take a mid-sized financial institution I worked with last year. Their TLS handshakes used RSA, which they knew was vulnerable. The fix wasn’t upgrading servers-it was auditing every transaction path to identify quantum-resistant alternatives before a breach exposed their entire infrastructure.
Here’s the kicker: post-quantum cryptography isn’t a monolith. It’s a spectrum of algorithms designed to survive quantum attacks. Lattice-based crypto (like Kyber) is currently the frontrunner because it’s versatile-secure for both encryption *and* digital signatures. Hash-based schemes (like SPHINCS+) offer theoretical elegance but face performance hurdles. And then there’s code-based crypto, which was once considered bulletproof-until quantum error correction made it shakier.
Hybrid systems: The pragmatic middle ground
Most organizations aren’t jumping to post-quantum overnight. That’s why hybrid approaches are winning. IBM’s tools let companies layer post-quantum cryptography onto existing RSA/ECC systems, creating a buffer until they’re ready to switch entirely. For example, a client I advised replaced only their TLS certificates with Kyber while keeping RSA for internal authentication. The result? No downtime, but a quantum-ready skeleton. Yet here’s the catch: post-quantum cryptography isn’t just about tech. It’s about culture. I’ve seen teams freeze when they realize their PKI (Public Key Infrastructure) relies on RSA-something that could become obsolete overnight. The real fight isn’t technical; it’s organizational.
- Assess risk: Identify which systems handle critical data (think defense contracts or blockchain transactions).
- Pilot post-quantum: Test Kyber or Dilithium in low-stakes areas first.
- Incremental replace: Swap components like TLS certificates before overhauling legacy systems.
The gaps no one’s talking about
Here’s the harsh truth: the world isn’t ready. Standardization is still catching up-NIST’s finalists are out, but adoption lags. Performance penalties are real: lattice-based crypto is slower than RSA. And legacy systems? Forget it. Many organizations run on mainframes with 20-year-old crypto. Upgrading them is like rewiring a house while the family’s inside.
Yet the urgency isn’t just about theoretical attacks. A nation-state with a quantum-resistant backdoor today could compromise your systems before anyone notices. The NSA’s 2030 deadline isn’t a suggestion-it’s a warning. Companies that wait until quantum computers arrive will be playing catch-up. I’ve seen firsthand how quickly compliance deadlines turn from optional to existential. The question isn’t *if* you’ll need post-quantum cryptography-it’s *when* you’ll regret not starting.
This collaboration between Bain and IBM isn’t just about technology. It’s about recognizing that security isn’t static. It’s a living system that demands constant adaptation. The experts aren’t just warning us anymore-they’re building the future, one algorithm at a time. And if history’s any indicator, the companies that act now will write the next chapter. The rest? They’ll be reading about it in the headlines.